Attack Surface Infiltrates.
This isn’t a drill. The fundamental boundary that has defined application security for decades — the HTTP request — is rapidly becoming obsolete for a new generation of software: AI agents.
As these agents take on increasingly sophisticated tasks—reading files, scraping web pages, processing message queues—they operate in domains that bypass the traditional security checkpoints like Web Application Firewalls (WAFs) and proxies. This is precisely the gap Arcjet aims to fill with its latest offering, Guards.
The Evolving Threat Landscape
Arcjet, a runtime security firm based in San Francisco, has announced Guards, a new feature designed to enforce security policies not at the network edge, but inside the execution paths of AI agents. This includes tool handlers, queue consumers, and workflow steps—code segments that, crucially, never touch an HTTP request, rendering them invisible to conventional security tools. David Mytton, Arcjet’s CEO, explained this critical shift to The New Stack, highlighting how this inner perimeter is the new battleground.
The core problem is simple: traditional security tools operate on the assumption of a clear request boundary. An HTTP request arrives, gets vetted by middleware, and then proceeds to the application. This model, Mytton notes, was effective when applications had a single, well-defined entry point.
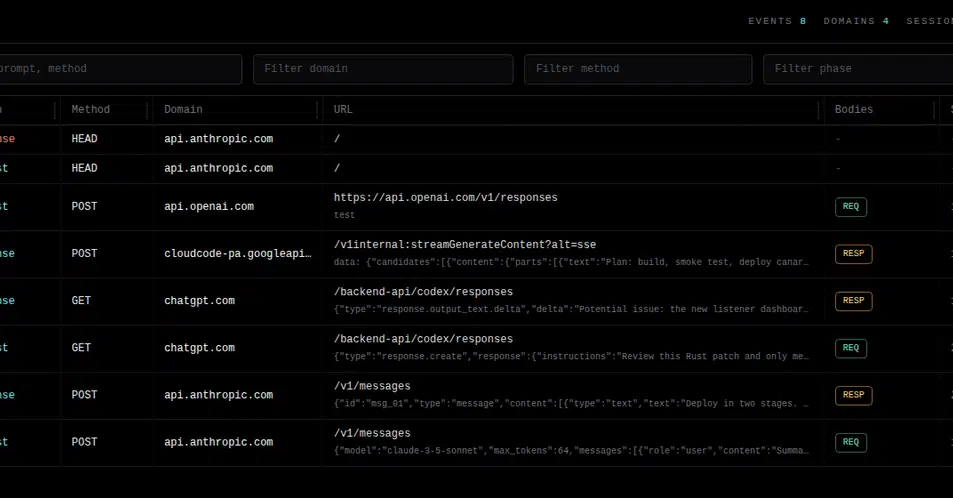
Agentic systems, however, don’t play by these rules. As Mytton articulated in a blog post, “An agent tool handler receives untrusted input as a function argument, not a request body.” Similarly, a queue consumer processes messages directly from a broker, bypassing any routing logic. Multi-agent pipelines shuffle state through shared memory or workflow engines, none of which involve crossing a network boundary that a proxy can monitor. The consequences, as we’re beginning to see, are substantial and often insidious.
Mytton cited a chilling real-world incident where an agent downloaded a malicious website. This site then instructed the agent to exfiltrate data to an external attacker. The WAF guarding the chatbot interface, the system’s supposed front door, remained oblivious. The attack vector wasn’t the chat interface itself, but the agent acting behind the scenes, manipulated through prompt injection. Even seemingly innocuous elements, like text instructions hidden within an image file an agent processes, can become vectors for compromise.
Beyond mere visibility, there’s a critical context deficit. While a proxy might see an incoming request, it has no insight into the user’s identity, their active session, the underlying business logic, or available budgetary constraints. Guards, by operating within the application’s runtime, has access to this vital context. In agentic systems, this lack of visibility is amplified, as a proxy cannot even recognize a tool call as distinct from a standard request.
Security Where the Code Lives
Guards integrates with Arcjet’s established SDK model, allowing developers to define security rules directly within the application codebase—the same place where the features themselves are written. This ensures that security measures are bundled with the code, subjected to the same scrutiny during code reviews and pull requests. The enforcement point is thus relocated to wherever untrusted input actually lands.
“Security has to live where the code lives,” Mytton stated in a press release. “For agentic systems, that means inside the tool calls and workflow steps where untrusted input actually arrives, not at a perimeter that no longer exists. Guards give developers a way to enforce policy inside the code paths agents use every day — the same place the threat model now lives.”
Initially, Guards targets three high-priority use cases for production agentic systems: detecting prompt injection within tool results (neutralizing malicious instructions before they re-enter the model’s context), blocking Personally Identifiable Information (PII) in tool inputs and queue messages destined for third-party models, and enforcing per-user token budgets within agent loops. The last point is particularly significant; Mytton was candid about the potential for runaway agent loops to incur substantial costs, stating that budget control is essential to prevent agents from “read[ing] thousands and thousands of pages and cost loads of money.”
Guards also offers a sophisticated approach to multi-agent scenarios. Instead of analyzing individual tool calls in isolation, it maintains session context throughout the entire pipeline. This means that as multiple agents collaborate on a task, each tool call is protected, and its output is subsequently analyzed, providing a layered defense.
Agent-First, Not Merely Agent-Friendly
Arcjet’s strategy extends beyond mere technical implementation. Mytton emphasizes the distinction between products that are merely “agent-friendly” and those built from the ground up with an “agent-first” philosophy.
“Being agent-friendly isn’t the same thing as being agent-first,” he wrote. “Shipping a CLI or an MCP server on top of an existing control plane or dashboard makes that control plane accessible to an agent, but that’s only half of the work.”
The other half, as Arcjet sees it, involves integrating directly into the agent’s operational environment—within the repository, embedded in the code, and part of the diff generation process. This deep integration means that the agent writing the chat handler can see the prompt injection rules protecting it, literally lines above in the same file. The code review encompasses both feature and security. The pull request that introduces new functionality also brings the associated protections, a model that feels less like an add-on and more like an intrinsic part of the development lifecycle.
This is a crucial distinction. If traditional security tools are like castle walls, Arcjet’s Guards are the vigilant guards patrolling the inner courtyards and hallways. The attack surface hasn’t just moved; it’s gone internal. And Arcjet’s strategy appears to follow suit, embedding its defenses directly into the operational heart of AI agents.